We have received reports from New Tripoli Bank customers that they have been contacted by unidentified individuals claiming to be employees of New Tripoli Bank. Moreover, the phone number that appears when customers are contacted is our customer service number. These individuals are contacting customers asking for personal or bank account information, or trying to initiate wire transfers. THIS IS A SCAM!
Please keep the following in mind:
- New Tripoli Bank will never contact you in order to ask for personal or bank account information.
- You should never initiate a wire transfer with anyone who you have not met in person or whose identity you are unable to verify.
If you or someone you know is contacted (via phone, text, email, etc.) by individuals claiming to be from New Tripoli Bank, please hang up immediately and contact our security team at (610) 395-8834 to report the incident. We take our customers' security very seriously and we are looking into this matter to ensure we continue to protect our customers from potential fraud.
We have been alerted to a new type of phishing attack targeting consumers which involves attackers sending fake calendar invites to users' email accounts. These attacks take advantage of Google's default settings that automatically add invitations to your email calendar.
What is the attack
This phishing technique uses Google Calendar invitations to deliver scams directly to your calendar. Because Google automatically adds calendar invites by default, attackers can make these events appear genuine, showing them alongside your real meetings.
Common examples of fake calendar events include:
- “Your password is expiring – verify immediately”
- “Security alert: unauthorized login detected”
- “Invoice processed – payment confirmation”
- “Prize notification – claim your reward now”
Here is an example:
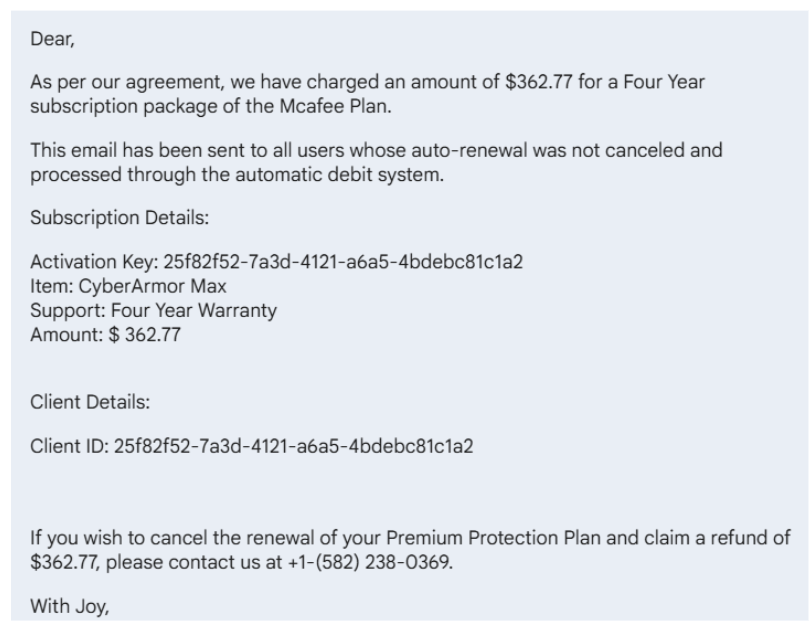
Attackers exploit Google’s default setting that automatically adds new calendar invitations to your schedule. When a user receives an invite, even from an unknown sender the event appears in their calendar, often with an urgent message in the description.
These descriptions can contain:
- Fake phone numbers claiming to connect to support or billing departments
- Malicious links to phishing websites or fake login pages
- Urgent or alarming messages designed to prompt quick action
Once a user clicks a link or calls the number, the attacker can try to steal login credentials, financial information, or remote access to the computer.
The Attacker's Goal
Attackers disguise their phishing lure as a harmless calendar event to get your attention. The attacker’s goal is to get you to contact them, where the real attack occurs. They will attempt to extract credit card details or login information if you call the phone number or click any links.
By exploiting a familiar platform you use daily and naturally consider safe, such as Google Calendar to take advantage of the false sense of security you may feel when using it.
Red Flags
Watch for these red flags in suspicious calendar invitations:
- Titles can reference anything but focus on invoices and calls to action. These types of invite titles can look more like email titles. Following are some examples:
- “Processing Complete: Bill INV936377”
- “Your password is expiring – verify immediately”
- “Prize notification – claim your reward now”
- The organizer is not someone you know.
- The event description can often include a phone number to “cancel” or “secure a refund” or a malicious link they want you to use.
What to Do if You Receive a Suspicious Google Calendar Invite
- Report and delete the event. Use Google’s “Report Spam” feature
- Do not engage. Never click links, call phone numbers, or reply to a suspicious event because they could get access to your personal or business-related information.
- Do not select “Accept” or “Decline”. This confirms your email address is active and can lead to more spam.
How to Potentially Prevent Future Calendar Scams
Some people put in higher levels of protection by limiting who can add events to your Google Calendar. To do this, follow these steps:
- Open Google Calendar in your web browser.
- Click the gear icon in the upper-right corner and select Settings
- In the left-hand menu, choose Event settings.
- Under “Add invitations to my calendar,” select either:
- Only if the sender is known, or
- When I respond to the invitation email.
However, there are downsides to creating this level of protection. While limiting who can automatically add events to your calendar helps protect against phishing scams, it may also change how legitimate invitations behave.
- Legitimate invites might not appear automatically.
- You might need to manually accept more invites: You’ll have to open the invitation email and click “Yes” to add it, which adds an extra step for meetings, especially from external partners or conference organizers.
For some, the benefits outweigh the drawbacks for most users, especially given the rise of calendar-based phishing attacks, but it’s important to understand that you’re trading a bit of convenience for added protection.
If you frequently collaborate with external partners, you can balance security and usability by choosing “Only if the sender is known” (rather than the stricter “When I respond”) and staying vigilant when reviewing event emails.
New Tripoli Bank is always tracking new and novel tactics that fraudsters are using in order to deceive consumers, so we can keep our customers informed and protected. Recently we have heard reports of a new scam which targets recipients of Paycheck Protection Program (PPP) loans, exploiting publicly-available PPP loan data to deceive individuals into revealing sensitive personal and financial information.
These scams often involve the fraudsters impersonating employees of financial institutions or the U.S. Treasury, up to and including spoofing the phone numbers of actual organizations to make it appear as though their calls are coming from a legitimate source. Upon making contact with their target, these scammers request online banking credentials and one-time security codes which they use to access accounts and initiate unauthorized transactions.
How the Scam Works
Common Methods of Contact
- Spoofed phone numbers: The call might appear to come from a legitimate bank phone number.
- Text messages: The fraudsters may contact your personal mobile phone number via text message.
Reasons for Contact
Fraudsters will make up a convincing excuse as to why they are asking for personal information. Regardless of the stated reason that you are being contacted, you should always be suspicious of anyone who asks about bank information or transactions.
Some stated reasons they may use include:
- Issues with a payment or transaction on your account.
- Suspicious account activity or potential fraud.
Asking for Information
If someone calls you and asks for the following information, this is an immediate red flag that you are being targeted by a scam.
- Requests for your online banking credentials or security tokens.
- Asking you to click on a link in order to "update" your digital banking information or to "freeze" a transaction.
Protect Yourself!
You are the first line of defense against frauds and scams, and your strongest weapon is information. Trust your intuition—if you're unsure about the veracity of someone claiming to be from the bank or the U.S. government, you can always hang up and call back at an official number posted on your bank's website or the official website of the government agency. Remember that an employee of the bank or government will already have your account information.
- Don't Trust Caller ID: Phone numbers can be spoofed. You should independently verify the caller's identity and hang up if you encounter anything suspicious.
- Verify Callers: If you receive a suspicious phone call from someone claiming to be from New Tripoli Bank, hang up and call us directly at (888) 298-8821.
- Don't Click Links! Never click on a hyperlink from a sender you do not recognize.
- Don't Share Your Information: Never share personal identifying information, bank account information, login credentials, tokens, or passwords.
- Educate Others: You are most likely not the only person being targeted by scammers. If you know others who may be targeted, share this information with them so they can avoid being scammed as well.
- Report Suspicious Activity: If you are the target of a scam attempt, contact our security team at (610) 421-4001 or visit our Contact Us page.
We Want to Help!
If you have any concerns or believe you may have been targeted by a scam, please contact your local New Tripoli Bank branch office, loan officer, and our security team immediately. Even if you are unsure, we prefer that you take extra precautions rather than fall victim to fraud. Your personal and financial security is our top priority.
When hiring an individual or firm to prepare a tax return, you need to understand who you're choosing and what important questions to ask. Even though most tax return preparers provide honest, quality service, some may cause harm through fraud, identity theft and other scams.
Your needs determine which kind of preparer is best for you. Whether you regularly use a tax professional to help you file a tax return or have decided to work with one for the first time, choosing a tax professional carefully is important. You are ultimately responsible for all the information on your income tax return, regardless of who prepares it.
Warning signs
By law, anyone who is paid to prepare or assists in preparing federal tax returns must have a valid Preparer Tax Identification Number. Paid preparers must sign and include their PTIN on any tax return they prepare.
Not signing a return is a red flag that the paid preparer may be looking to make a quick profit by promising a big refund or charging fees based on the size of the refund. Taxpayers should avoid these unethical "ghost" tax return preparers.
A ghost preparer is someone who doesn't sign tax returns they prepare. Unscrupulous ghost preparers often print the return and have the taxpayer sign and mail it to the IRS. For electronically filed returns, a ghost preparer will prepare the tax return but refuse to digitally sign it as the paid preparer.
Tips for selecting a tax return preparer
Here are a few tips to consider when choosing a tax return preparer:
- Look for a preparer who's available year-round. If questions come up about a tax return, you may need to contact the preparer after the filing season is over.
- Review the preparer's history. Check the Better Business Bureau website for information about the preparer. Look for disciplinary actions and the license status for credentialed preparers. For CPAs, check the State Board of Accountancy's website, and for attorneys check with the State Bar Association. For enrolled agents go to Verify the Status of an Enrolled Agent or check the IRS Directory of Federal Tax Return Preparers.
- Ask about service fees. You should avoid tax return preparers who base their fees on a percentage of the refund or who offer to deposit all or part of the refund into their own financial accounts. Be wary of tax return preparers who claim they can get larger refunds than their competitors.
- Ensure their preparer offers IRS e-file. The IRS issues most refunds in fewer than 21 days for taxpayers who file electronically and choose direct deposit.
- Provide records and receipts. Good preparers ask to see these documents. They'll also ask questions to determine your total income, deductions, tax credits and other items. Do not hire a preparer who e-files a tax return using a pay stub instead of a Form W-2. This is against IRS e-file rules.
- Understand the preparer's credentials and qualifications. Attorneys, CPAs and enrolled agents can represent any client before the IRS in any situation. Annual Filing Season Program participants may represent taxpayers in limited situations if they prepared and signed the tax return.
- Never sign a blank or incomplete return. Taxpayers are responsible for filing a complete and correct tax return.
- Review the tax return before signing it. Be sure to ask questions if something is not clear or appears inaccurate. Any refund should go directly to you – not into the preparer's bank account. Review the routing and bank account number on the completed return and make sure it's accurate.
You can report preparer misconduct to the IRS using Form 14157, Complaint: Tax Return Preparer PDF. If you suspect a tax return preparer filed or changed your tax return without your consent, you should file Form 14157-A, Tax Return Preparer Fraud or Misconduct Affidavit PDF.
When choosing a tax professional, the IRS urges taxpayers to visit IRS.gov. The Choosing a Tax Professional page has information about tax return preparer credentials and qualifications. The IRS Directory of Federal Tax Return Preparers with Credentials and Select Qualifications can help identify many preparers by type of credential or qualification.
This information was provided by the Internal Revenue Service.
Payment cards are exceptionally convenient for consumers, and they come in various types –ATM, credit, debit, EBT – that enable low-friction banking and shopping. You probably use more than one. But you may not be aware of the various scams and tools fraudsters use to steal your payment information at the terminal and convert it into a substantial payday. It only takes seconds to install a scam device, and they can be anywhere. Fortunately, it takes even less time to protect your ATM and payment card.
Scam Devices
Scam devices have been found on ATMs, Point of Sale (POS) terminals, gasoline pumps – everywhere people use a card to pay. These devices capture personal data and PINs via video, digital download, or wireless transmission to the scammer. For example:
- Pinhole cameras are installed to record PIN entries and are so small they’re hard to detect. Note that pinhole cameras may be placed anywhere on or near the machine.
- Skimmers installed in the terminal or over its reader steal credit/debit card data from the magnetic stripe or chip.
- Keylogging keypads are overlays that cover the real keyboard, used to record a customer’s keystrokes. If the criminal knows what you type, they know your PIN.
Protecting Your Payment Card
- Inspect ATMs, POS terminals, and other card readers for loose, crooked, damaged, or scratched parts. If you notice something suspicious, use a different terminal.
- Check for keylogging overlays by lifting the edge of the keypad – a gentle tug is all it takes.
- Prevent cameras from recording your PIN by shielding your entry with your hand. Keep in mind that a pinhole camera may be present anywhere on or around the terminal.
- If possible, use ATMs in well-lit, high-traffic locations. Machines are less vulnerable in places where someone might notice a threat actor tampering with them.
- Be especially alert for skimming devices in tourist areas, where card readers are used a lot.
- When possible, use debit and credit cards with chip technology rather than magnetic stripes, which are more vulnerable to theft.
- Avoid using your debit cards for multiple accounts – the compromise of one card gives criminals access to all the accounts. Use a credit card instead.
- Routinely monitor your card accounts to promptly identify any unauthorized transactions. If possible, set up email or text-message alerts to notify you of account transactions.
- Proactively review the account security options. You may be able to set up multifactor authentication or freeze an account between transactions. Such steps may seem inconvenient, but they significantly reduce the risk of financial losses.
- Never give your PIN in response to a call, text, or email. Organizations that have your information would not request your PIN. They use other means to authenticate your account. If you receive a request, look up the source’s website and contact them to check your account.
- Always use a strong PIN. Avoid using PINs that may be easily guessed, such as strings of the same or consecutive numbers (e.g., 11111 or 1234).
- Find out if your account will allow you to temporarily block or freeze transactions on the account.
Tips for Paying at the Pump
- Choose the fuel pump closest to the store and in direct view of the attendant. These pumps are less likely to be targets for skimmers.
- Run your debit card as a credit card. If that’s not an option, cover the keypad when you enter your PIN. You should also examine the keypad before use for any inconsistencies in coloring, material, or shape. These inconsistencies might suggest that a foreign device (keypad overlay) is present.
- Consider paying inside with the attendant, not outside at the pump.
- Tap the card instead of swiping or inserting it when paying at the pump (if the card and terminal allow for it). Tap-to-pay transactions are more secure and less susceptible to compromise.
What to do if You Are Scammed
- Contact your financial institution immediately if the ATM doesn't return your card after you finish or cancel a transaction. It may indicate a foreign device is in the card reader.
- If you suspect your card was compromised, immediately contact your state benefits agency or card issuer. Promptly change your PIN if any funds remain in your account.
If You’re a Victim?
Immediately change any passwords you might have revealed. Consider reporting the attack to IC3.gov and the police.
Phishing is a common tactic scammers use to trick consumers into willingly giving up personal information such as passwords, bank account numbers, or Social Security numbers. They do this by sending fraudulent emails or text messages posing as representatives of the bank, exploiting customers' trust to collect personal and financial information. With this information, they could gain access to your email, bank, or other accounts, or even sell the information to other scammers. Scammers also use phishing to trick consumers into clicking a link which will download malware onto their computers.
Scammers will update their tactics based on the latest news and trends, but no matter what form they take, there are always red flags you can look out for when you receive a message asking for personal information:
Spelling Errors. Many phishing emails and texts will contain numerous spelling errors and grammatical mistakes. Official company emails are reviewed multiple times before being sent to customers and will rarely contain large amounts of misspelled words or improper punctuation.
Generic Greetings. You should be suspicious of any email or text message that addresses you by the wrong name or does not use a proper name in its greeting.
Urgency. Phishing preys upon consumers who are prone to click before they think. These emails and text messages often tell a story to trick you into clicking on a link or opening an attachment. Some common messages scammers will use include:
- "We've noticed suspicious activity on your account."
- "There has been a problem with a recent payment and we need your account information."
- "You are eligible to register for federal loan payments."
- "You have a delinquent payment on your account. Click the link to update your payment information."
- "Your account will be locked if you do not verify your account information."
In all these examples, the scammers are creating a sense of potential future danger if you do not act quickly. You should always take the time to think before you click a link in a text message or email. More importantly, legitimate businesses will never ask you to provide personal or account information via email or text.
If you are worried one of these messages may be legitimate, you should reach out to your bank directly via their phone number listed on their website instead of clicking on a link or calling a number in an email or text message.
How to Protect Yourself
You can pre-emptively protect yourself from phishing attacks to minimize your risk of being scammed. Some good habits include:
- Install security software. Make sure your computer and your phone have security software installed.
- Set security software to update automatically. Security software is continually updated with the latest security threats. Check your software's settings to ensure that you have automatic updates enabled.
- Enable multi-factor authentication. Many companies now offer multi-factor authentication for their accounts, which requires additional security credentials to access. In addition to your username and password, multi-factor authentication can include security questions, one-time verification passcodes you receive by text, email, or from an authenticator app, a security key, or a scan of your fingerprint, retina, or face. These methods make it harder for scammers to log into your accounts if they manage to steal your personal information.
- Back up your data. Save a copy of your computer or phone data onto an external hard drive or to the cloud.
What to Do If You Suspect Phishing
If you receive a phishing email or text message, report it! This information helps your bank, law enforcement, and the government fight scammers.
Contact your bank to report the phishing attack, especially if you mistakenly gave any information to the scammers. The bank can help you lock down your accounts and issue you new cards so that the scammers won't be able to access your funds.
You should always file a police report if you are targeted by a scammer. Law enforcement keeps a record of these incidents which can help them spot patterns and potentially apprehend cybercriminals.
Report the phishing attempt to the FTC at ReportFraud.ftc.gov. You can forward phishing emails to the Anti-Phishing Working Group at reportphishing@apwg.org and you can forward phishing text messages to SPAM (7726).
Lastly, review your credit reports and put a security freeze on. This can be done proactively as a consumer.
We have received reports from New Tripoli Bank customers that they have been contacted by unidentified individuals claiming to be employees of New Tripoli Bank. Moreover, the phone number that appears when customers are contacted is our customer service number. These individuals are contacting customers asking for personal or bank account information, or trying to initiate wire transfers. THIS IS A SCAM!
Please keep the following in mind:
- New Tripoli Bank will never contact you in order to ask for personal or bank account information.
- You should never initiate a wire transfer with anyone who you have not met in person or whose identity you are unable to verify.
If you or someone you know is contacted (via phone, text, email, etc.) by individuals claiming to be from New Tripoli Bank, please hang up immediately and contact our security team at (610) 395-8834 to report the incident. We take our customers' security very seriously and we are looking into this matter to ensure we continue to protect our customers from potential fraud.
If you and your children have a mobile phone, you’ve probably received texts from friends and family. If you’ve opted in to receive texts from retailers, you get these too. But what do you do when you receive a text, and you question the source?
The answer matters because your response to a questionable text might keep you safe from a scammer — or lead you into a trap.
Text Message Scams on the Rise
New data from the Federal Trade Commission (FTC) shows that in 2024, “consumers reported losing $470 million to scams that started with text messages. This amount is five times higher than what was reported in 2020, even though the number of reports declined.”
How Text Scams Work
Below is a simplistic example of how a spoofed message can be sent to you.
Step One. Threat actors obtain your phone number on the Dark Web or generate your number with an auto-dialer tool.
Step Two. The scammer creates a message. Many scam texts sound urgent to get victims to react without thinking — “invoice overdue” or “your account has been breached” are common ruses.
Step Three. The scammer sends the text and hopes you bite.
Prevention Tips
- Don’t reply to unexpected text messages. The text may push you to react quickly, but it’s best to stop and think it through.
- Never click links in unexpected messages. You might download malicious software (malware) that will compromise your device, and scammers often create real-looking websites to draw you deeper into the trap.
- Don’t assume a text from a known company or organization is legit. Double-check by contacting the company. Don’t use information from the text — get a phone number or email address from the company’s website.
Filtering Unwanted Texts
There are many ways to filter unwanted text messages or stop them before they reach you.
| On your phone | Your phone may have an option to filter and block spam or messages from unknown senders. Here’s how to filter and block messages on an iPhone and how to block a phone number on an Android phone. |
| Through your wireless provider | Your wireless provider might have a tool or service that lets you block calls and text messages. Check out ctia.org, a website from the wireless industry, to learn about options from different providers. |
| With a call-blocking app | Go to ctia.org for a list of call-blocking apps for Android, BlackBerry, Apple, and Windows phones, or search for an app online. Check out the features, user ratings, and expert reviews. |
Take Action – Report Texts
- Forward spam messages to 7726 (SPAM). This helps your wireless provider spot and block similar messages.
- Report potential scams on either the Apple iMessages app or Google Messages app for Android users.
- Report potential scams to the FTC at ReportFraud.ftc.gov.
If you’ve lost money to a scam, reach out to the company that transferred the money right away to see if there’s a way to get your money back. Then report the scammer at ReportFraud.ftc.gov.
If You’re a Victim?
Immediately change any passwords you might have revealed. Consider reporting the attack to IC3.gov and the police, and file a report with the Federal Trade Commission.
Getting Help
If you identify suspicious activity involving your financial institution, contact them immediately.
*Information provided by the Financial Services Information Sharing and Analysis Center (FS-ISAC).
In order to combat a rise in property and mortgage fraud in Lehigh County, the Clerk of Judicial Records has released a new, free alert system for residents of Lehigh County.
The program is called Record Alert and it allows any resident in the county, or anyone with property in Lehigh County, to receive alerts via text or email when a document is recorded involving their property.
The Recorder of Deeds office is required to record any document that is presented to their office when all the required data is properly executed and payment is received alongside the document. Once a fraudulent document is recorded, the fraudster may use your name as collateral on a mortgage or attempt to sell your home to an unsuspecting buyer. There is no way for the Recorder of Deeds office to know that the document is being used for fraudulent purposes without being alerted by the legitimate property owner.
By registering for Record Alert, you will receive alerts when a document is recorded which involves your property. The notification will come via text or email stating the parcel number, instrument number, document type, and the date it was recorded. You can then contact the Recorder of Deeds and inform them of the fraudulent document before the criminal can use your name or property.
This service also allows you to monitor the status of legitimate documents that you've filed with Lehigh County, such as after you finish with a closing, or when you take out or pay off a mortgage.
Residents of Lehigh County can register for this free service at https://www.landex.com/recordalert/lehigh
Tax Day is fast approaching and with it, scammers are crawling out of the woodwork to cheat honest taxpayers out of their money.
Remember the old adage: "If it sounds too good to be true, it probably is!" Steer clear of anyone offering a way to "cheat" the tax system to get rich quick or avoid your obligation as a citizen of the United States to file your tax return and pay any outstanding taxes. Some of these schemes can literally cost you your life savings, while others can result in prosecution or imprisonment if you knowingly participate in them.
Abusive Return Preparer
Be very careful when selecting a business to help prepare your taxes. While there are plenty of reputable tax professionals that offer excellent service for their clients, there will inevitably be a few bad eggs who file false or fraudulent tax returns in order to defraud their clients.
Even if someone else prepares your return, the final responsibility for the accuracy of your tax return ultimately falls upon you. Check the credentials of your tax professional before relying on them to prepare you returns. Some red flags to watch out for include:
- A preparer asks for cash-only payment without providing a receipt.
- They claim fake deductions to inflate the size of your refund.
- The preparer invents false income in order to get their client more tax credits.
- They prepare your tax return but refuse to sign or include their IRS Preparer Tax Identification Number.
- Your refund is directed into their bank account rather than yours.
Abusive Tax Schemes
Anyone who browses social media for any amount of time will encounter people claiming they know a "cheat" or "workaround" that consumers can use to avoid paying taxes or to obtain a tax benefit. These schemes can take many forms, including:
- Offshore Tax Havens - Fraudsters create shell companies or trusts in these "tax havens" to hide income and assets offshore. These can also take the form of bank accounts in offshore tax havens, or money invested into digital assets such as cryptocurrency.
- Loan Schemes - Directors receive their income in the form of loans without any intention of ever repaying the loan, in order to avoid payroll taxes.
- Ponzi Schemes - Many Ponzi schemes claim the returns they generate are tax-free or that any losses you incur as part of a Ponzi scheme can offset your tax burden.
- Phantom Trusts - These are trusts set up for the sole purpose of claiming fraudulent deductions on tax returns in order to avoid paying taxes.
- Abusive Retirement Plans - These look like normal retirement plans but do not comply with tax laws, leading filers to claim improper deductions.
Non-Filer Enforcement
You may have come across a social media post or video featuring someone arguing that taxes are voluntary or illegal. They quote some part of the U.S. Constitution or U.S. Case Law to argue their point in order to bolster their argument.
Remember: you are (probably) not an attorney specializing in tax law, and this person making these claims most likely isn't either. Courts have repeatedly rejected these arguments as frivolous and routinely impose financial penalties for raising these arguments. Taxes are a mandatory part of living and working in the United States.
To help the public recognize and avoid abusive tax schemes, the IRS offers an materials for consumers to educate themselves. Familiarize yourself with the basics and report any suspicious activity to the IRS. You can learn more here: https://www.irs.gov/help/tax-scams/report-a-tax-scam-or-fraud
Next Page »
 Log In
Log In

 Log into Online Banking
Log into Online Banking